Setting up a MySQL Cluster on Google Platform Console using the Kubernetes MySQL Operator
Last week we took you throughout the entire process of setting up a Kubernetes MySQL Operator Cluster on Microsoft Azure—starting with installing or upgrading your Azure version, creating the very first cluster in Azure Container Service, to configuring and deploying the cluster to get it up and running. Today we continue our Kubernetes series with a matching tutorial, but for Google Platform Console, promising that by the end of this article, you will see your cluster in action and enjoy the resulting mix of these high-quality services working flawlessly together.
For more information visit the Kubernetes Engine Page in Google Platform Console.
#Kubernetes MySQL Operator Cluster Setup for GPC
Select or create a new project. For more information about creating a new project, check: Creating and Managing Projects.
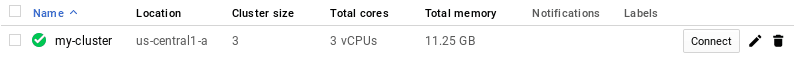
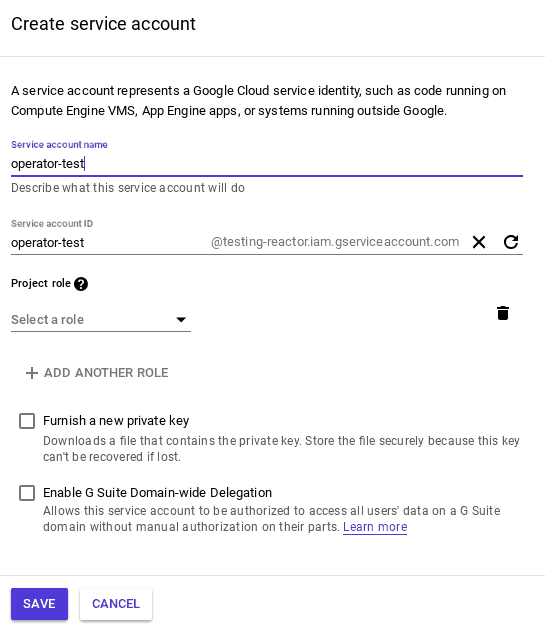
Select the Create Cluster button.
![]()
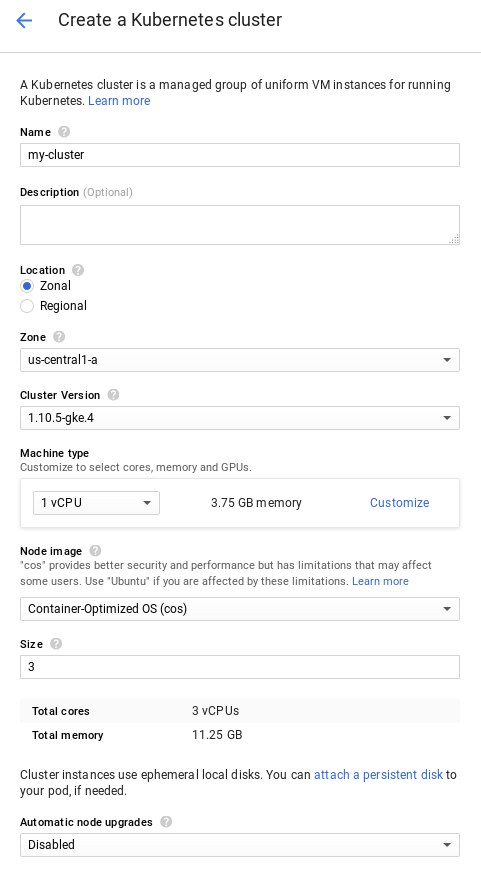
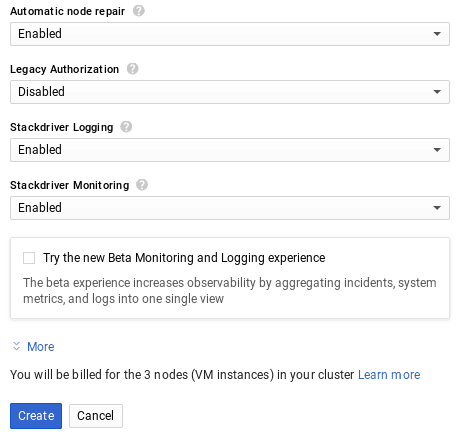
Complete the cluster information, then click Create.
Please note that you need to have gcloud installed on your computer. For more information on how to install gcloud check: gcloud Overview.
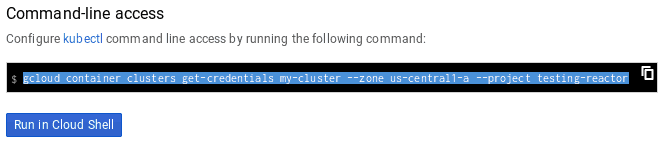
Next, connect to your Cluster. Select the Connect button.
Copy the command in a terminal or run the command in Cloud Shell
$ gcloud container clusters get-credentials my-cluster --zone us-central1-a --project testing-reactor
Fetching cluster endpoint and auth data.
kubeconfig entry generated for my-cluster.
You will now need to install kubectl. For more details, see: Install kubectl.
And helm, too. New to helm? Check Install Helm.
To verify your cluster connection, use the kubectl get command to return a list of the cluster nodes.
$ kubectl get nodes
NAME STATUS ROLES AGE VERSION
gke-my-cluster-default-pool-8e8240b1-1gd8 Ready none 23h v1.10.5-gke.4
gke-my-cluster-default-pool-8e8240b1-7ck1 Ready none 12h v1.10.5-gke.4
gke-my-cluster-default-pool-8e8240b1-mkg4 Ready none 7h v1.10.5-gke.4
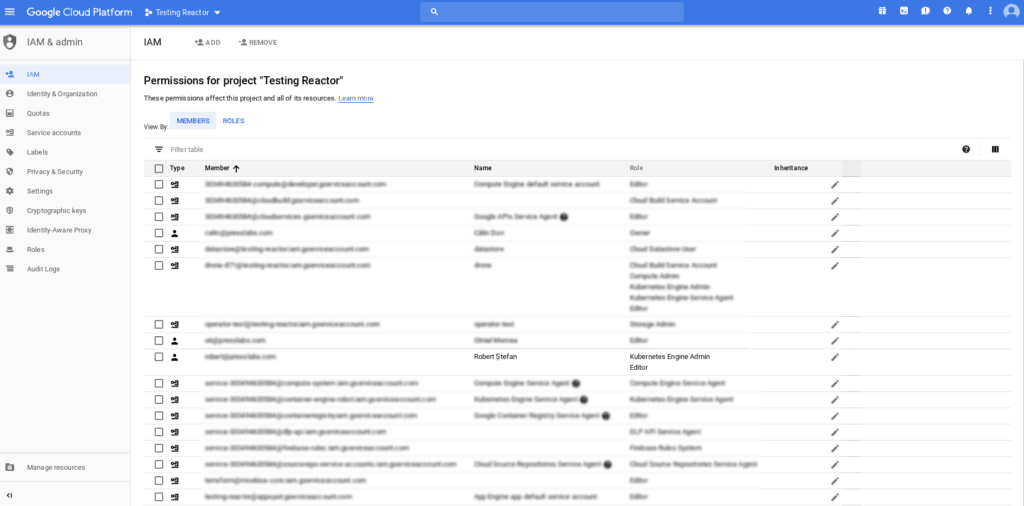
Note: You need to have Kubernetes Engine Admin permission.
To deploy this controller, use the provided helm chart by running:
$ kubectl create serviceaccount -n kube-system tiller
serviceaccount "tiller" created
$ kubectl create clusterrolebinding tiller-crule --clusterrole=cluster-admin --serviceaccount=kube-system:tiller
clusterrolebinding.rbac.authorization.k8s.io "tiller-crule" created
$ helm init --service-account tiller --wait
$HELM_HOME has been configured at /home/presslabs/.helm.
Tiller (the Helm server-side component) has been installed into your Kubernetes Cluster.
Please note: by default, Tiller is deployed with an insecure 'allow unauthenticated users' policy.
For more information on securing your installation see: https://docs.helm.sh/using_helm/#securing-your-helm-installation
Happy Helming!
$ helm repo add presslabs https://presslabs.github.io/charts
"presslabs" has been added to your repositories
$ helm install presslabs/mysql-operator --name mysql-operator
NAME: mysql-operator
LAST DEPLOYED: Tue Aug 14 15:50:42 2018
NAMESPACE: default
STATUS: DEPLOYED
...
For more information about chart values go to README. This will deploy the controller along with an orchestrator cluster.
Before creating a cluster, you need a secret that contains the ROOT_PASSWORD key. An example of this secret can be found in examples/example-cluster-secret.yaml. Create a file named example-cluster-secret.yaml and copy into it the following YAML code:
apiVersion: v1
kind: Secret
metadata:
name: my-secret
type: Opaque
data:
# root password is required to be specified
ROOT_PASSWORD: bm90LXNvLXNlY3VyZQ==
Note. ROOT_PASSWORD must be base64 encoded.
Now, to create a cluster you need just a simple YAML file that defines it. An example can be found in examples/example-cluster.yaml.
Create a file named example-cluster.yaml and copy into it the following YAML code:
apiVersion: mysql.presslabs.org/v1alpha1
kind: MysqlCluster
metadata:
name: my-cluster
spec:
replicas: 2
secretName: my-secret
For a more in-depth configuration, check our examples.
Deploying a cluster:
$ kubectl apply -f example-cluster-secret.yaml
secret "my-secret" created
$ kubectl apply -f example-cluster.yaml
mysqlcluster.mysql.presslabs.org "my-cluster" created
To list the deployed clusters, use:
$ kubectl get mysql
NAME AGE
my-cluster 1m
To check the cluster state, use:
$ kubectl describe mysql my-cluster
...
Status:
Ready Nodes: 1
Conditions:
Last Transition Time: 2018-08-16T11:28:14Z
Message: Cluster is not ready.
Reason: statefulset not ready
Status: False
Type: Ready
...
#Backups
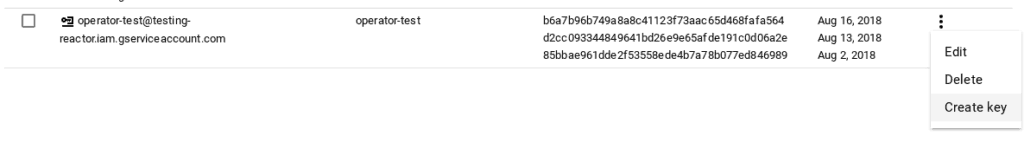
You need to create a service account. Go to Google Console -> IAM & Admin -> Service accounts.
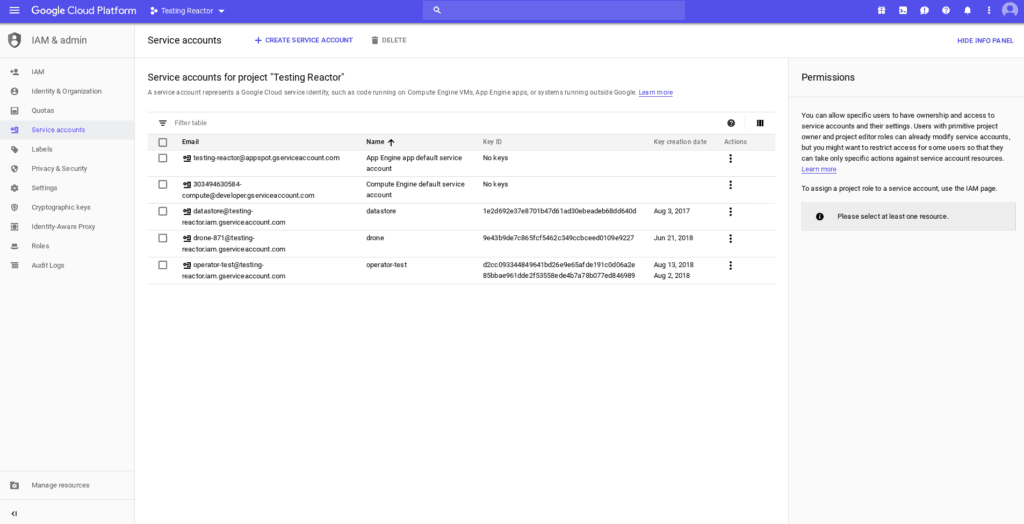
Click on Create Service Account.
![]()
Set the service account’s information, then click Save.
After that, select the Create key button to get the key for your service account.
You need to have a secret. Create a file named example-backup-secret.yaml and copy into it the following YAML code:
apiVersion: v1
kind: Secret
metadata:
name: my-cluster-backup-secret
type: Opaque
data:
GCS_SERVICE_ACCOUNT_JSON_KEY: #
GCS_PROJECT_ID: #
You need to complete the GCS_SERVICE_ACCOUNT_JSON_KEY field with the key you just downloaded; you also need to complete the GCS_PROJECT_ID field with your project’s name.
Note. GCS_SERVICE_ACCOUNT_JSON_KEY and GCS_PROJECT_ID must be base64 encoded.
Then run this command:
$ kubectl apply -f example-backup-secret.yaml
secret "my-cluster-backup-secret" created
Backups are stored on object storage services like S3 or Google Cloud storage. In order to be able to store backups, the secret defined under backupBucketSecretName must use credentials to store those backups.
Setup your backups to Google Cloud. You need to have a storage bucket. For more information, learn how to create a storage bucket.
Requesting a backup is easy. You just need to create a file named example-backup.yaml and copy into it the following YAML code:
apiVersion: mysql.presslabs.org/v1alpha1
kind: MysqlBackup
metadata:
name: my-cluster-backup
spec:
clusterName: my-cluster
Run the following command:
$ kubectl apply -f example-backup.yaml
mysqlbackup.mysql.presslabs.org "my-cluster-backup" created
You need to specify the backupBucketUri for the corresponding cluster to an URI like gs://BUCKET_NAME and backupSecretName
Open the file named example-cluster.yaml and copy into it the following YAML code:
apiVersion: mysql.presslabs.org/v1alpha1
kind: MysqlCluster
metadata:
name: my-cluster
spec:
replicas: 2
secretName: my-secret
backupSecretName: my-cluster-backup-secret
backupUri: gs://pl-test-mysql-operator/
Then run the following command:
$ kubectl apply -f example-cluster.yaml
mysqlcluster.mysql.presslabs.org "my-cluster" configured
To list all backups, use the kubectl get command to return a list of the backups.
$ kubectl get mysqlbackup
NAME AGE
my-cluster-backup 55s
To check the backup state, use kubectl describe command:
$ kubectl describe mysql my-cluster
...
Status:
Backup Uri: gs://pl-test-mysql-operator/
Completed: false
Conditions:
Last Transition Time: 2018-08-17T08:08:31Z
Message: First initialization of backup
Reason: set defaults
Status: Unknown
Type: Complete
...
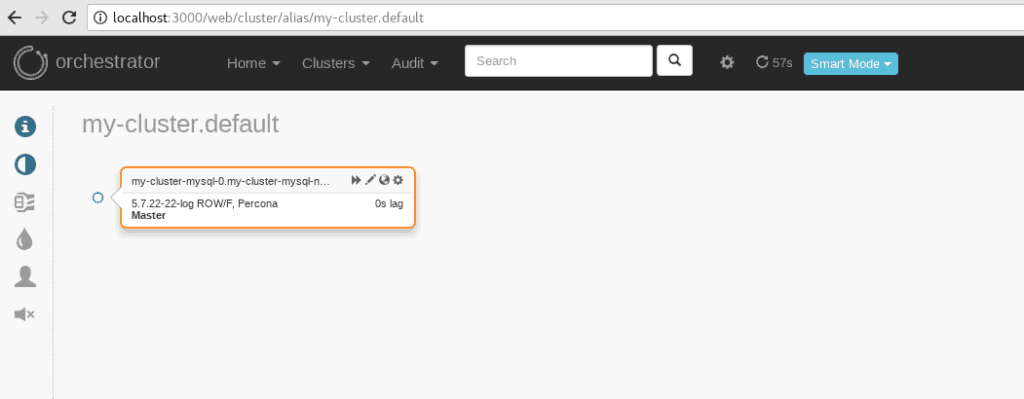
To connect to the orchestrator dashboard you have to port forward the orchestrator port 3000 to your local machine by using:
$ kubectl port-forward mysql-operator-orchestrator-0 3000
Forwarding from 127.0.0.1:3000 -> 3000
Forwarding from [::1]:3000 -> 3000
Type localhost:3000 in a browser.