Unless you’ve been living under a rock for the last month, you must have heard about the general commotion regarding personal data and how it’s exploited, for better or for worse. In this light, a new regulation is needed to better protect personal data against attacks and unethical mining.
Look no further than the EU’s General Data Protection Regulation, in short GDPR, which will bring a series of rules on how individual data is protected and processed. It will be enforced starting the 25th of this month and will have a major impact on all businesses around the globe.
In this blog post, we’re set on exploring all the facets of this regulation — in layman’s terms. We’ll explain what’s GDPR, what it entails and what you need to do to be compliant. This blog post was inspired by the GDPR Info website, where the legislation is presented for an enhanced understanding of this law and its impact. Let’s dive in.
#What’s GDPR?
The GDPR centers around imposing a set of rules with regard to processing and free movement of personal data of individuals residing in any country which is an EU member. This regulation applies to the processing of data in an automated way — either wholly, or partly.
You’d expect that only the businesses that have a physical presence in the EU will be the ones influenced by the regulation, but no. Any business that manages and processes data of an EU resident will have to comply with the same regulations, thus making a step forward in bringing a more streamlined and trustful process of handling personal data.
The GDPR initiative was first proposed in the European Parliament in 2012, and adopted in 2016, giving businesses and organizations four years to get ready to comply with the new rules. On May, 25th, the regulation will be enforced, and the magnitude of the impact will soon be measured.
#Controllers vs Processors
In this regulation, a distinction is made between the controller and the processor. The former determines the means and purposes of the processing the personal data, while the latter processes the personal data, on behalf of the controller.
The controller will need to provide guarantees that the processor implements appropriate technical and organizational measures, that comply with the regulation, supported by a legal act.
In this digital era, the controllers are the site owners — a business or an individual — and the processors are ranging from plugins to services and providers you give the individual’s data to hosting providers, analytics, marketing company, or email newsletter provider.
#Processors and controllers based outside of the EU
The transfer of personal data to a third country, meaning an organization outside the EU zone, will be permitted if the organization has an appropriate level of protection.
The processors and controllers that are based outside the EU will have to comply to the same rules as the EU organizations, and also to respect the same individual rights. When collecting data, the individual needs to give a recorded explicit consent.
#The individual’s rights
The GDPR states a series of rights that each individual has in terms of personal data — giving it a better control and knowledge of what kind of data and how is the data being processed and manipulated. The rights are as follows:
- The right of access. The individual will have the right to obtain from the controller information whether his personal data is being processed, the purpose of processing, the type of data being processed, if possible — the period of storage, and the existence of a right to request rectification or erasure of personal data.
- The right to rectification. The individual will have the right to obtain from the controller the rectification of inaccurate personal data concerning him, without any delay.
- The right to erasure. Also known as the right to be forgotten, the individual will have the right to obtain from the controller his data, and the controller to erase all personal data if the personal data is no longer necessary in relation to why it was processed in the first place, or the individual withdraws consent, or if the data has been unlawfully processed, among others. The controller will be obliged to erase the data, taking reasonable steps in accounts of available technology and cost of implementation, and inform processors the individual requested the erasure.
- The right to the restriction of processing. The individual will have the right to obtain from the controller the restriction of processing if the data accuracy is contested by the individual, or the processing is unlawful and the individual opposes erasure, or the controller doesn’t need the personal data, among others.
- The right to data portability. The individual will have the right to receive all his concerning personal data, in a structured and machine-readable format.
- The right to object. The individual will have the right to object at any time the processing of his personal data. The controller will have to stop processing the data unless he demonstrates compelling reasons which override the individual’s interests and rights.
#Breaches
In the worst case scenario, when the individual data is stolen or manipulated, the controller needs to inform them — in case the breach was a high risk. Furthermore, when the breach can result in a violation of the rights and freedoms of the individual, the controller needs to inform him directly.
There are situations which the individual doesn’t need to be informed, like when the controller implemented necessary protection measure to that data, and aren’t intelligible to another person, or when the high risk isn’t likely to materialize, or it would involve an immense effort — then a public statement will be issued.
#Penalties
Every individual will have the right to file a complaint with a competent institution if his rights have been violated. If the competent institution will find that the individual suffered material or non-material damage, the individual will have to receive compensation from the controller or the processor.
Depending on the violated rights, the controller or processor can be fined up to 20 000 000 EUR, or in case if an undertaking, up to 4% of the total worldwide annual turnover of the preceding financial year, whichever is higher.
#What qualifies as protected data?
Data is at the forefront of this legislation, and knowing exactly what needs to be protected, and how it needs to be safeguarded, is essential. At a first glance, we know that we need to protect data that comes from viewers, newsletter subscribers, CRM clients, or job applicants. But what exactly do we need to protect?
We’ve compiled a list of categories that exist in the aforementioned data comings and goings. These are the following:
- Contact and registration details such as first name, last name, email, username, and password
- Technical details like web applications, interactions with a service, IP address, browser type, browser language, browser language, date and time of the request
- Contact and bank details
- Tax and pension details
- Pay, annual leave, and performance details
- Medical leave details
- Contact, qualifications, employment details.
#WordPress sites and GDPR
WordPress is taking measures to help site owners and publishers get their sites ready to comply with the GDPR. They’ve formed a GDPR Compliance Team to focus on creating a functionality for site owners to construct privacy policies, creating guidelines for plugins, adding administration tools to encourage privacy, and adding documentation to educate site owners and publishers. Moreover, they will add a series of pages and fields like ‘postbox’ or ‘Privacy Page’ to better manage and protect personal data. Check out their roadmap for more information.
A WordPress site will usually collect personal data like IP addresses, names, physical addresses, and emails. There are numerous places where this kind of data is stored, and depending on your type of site, you should look into:
- Access Logs. IP addresses are displayed here, and it is the job of processors, meaning the hosting companies, to take care of anonymizing them. Here at Presslabs, we’ve undergone certain procedures to remove the displaying of IPs. Thus, in our Logs section, you’ll no longer see IPs.
- Analytics Tools. Google Analytics collects user information like IP addresses to detect the location, and browser settings to detect the language. In order to anonymize the IP addresses, you need to add an anonymizing object method. Furthermore, you can set the data retention time frame from 14 months to 50 months. Hotjar collects data movement and browser type, retaining the information for 365 days. IP addresses are suppressed before being stored.
- Contact Forms. Depending on the data you need from a form, it can contain username, email, address, a message, and other sensitive information. Contact Form 7 stores the data as a custom post, with the post type wpcf7_contact_form. This kind of data can be exported via Tools > Export.
- Product Orders. In case of WooCommerce sites, the data types that are introduced are email, password, physical address, payment method, and telephone number. Another key area to investigate is abandoned checkouts and the time frame for keeping that kind of information. These types of information are stored in a WooCommerce object. WooCommerce has compiled a list of a site owner’s obligations which is worth checking out.
- User Profile Data. Here, we talk about authentication credentials, in case of forums, information regarding comments, or subscriber information. For the first type, we talk about email, password, and username; for the second type, we talk about email and/or username, and for the latter type, we talk about email.
- Site Backups. The data included in site backups are user profile data, product orders, and contact forms. Thus, it is important to be careful when handling them.
#Emphasizing Analytics Tools
Having quantifiable data to see the progress of your site is key to understanding how your site is working. Tools like Google Analytics and Hotjar provide the aforementioned benefit. In GDPR terms, these tools are your data processors, and they need to comply to the legislature.
Both brands have started working on becoming GDPR compliant, Hotjar compiling a checklist of things to do, while Google has pledged a commitment to GDPR, by providing user transparency and a CMO checklist, among others. Moreover, publishers, as controllers, need to be informed of the body of work of the processors in terms of data handling. After this step, you will need to:
- Inform your users and viewers that their actions need to be tracked on the site for statistical reasons.
- Ask for consent for analyzing traffic and storing it.
#Is GDPR is a good thing?
Yes, it definitely is. For a long time, companies and organizations had an easy time in collecting user information, with which will target specific ads or some unethical actions like manipulating the point of view of a group. This will change when GDPR will be enforced.
This regulation was compiled with the end user in mind, to protect their privacy. It will be an opportunity to create trust between brands and consumers and ensure a better transfer of services.
#How to become GDPR compliant
There are some steps for publishers(controllers) to take into consideration in order to become GDPR compliant, thus, we compiled a GDPR checklist. You should do the following:
- Organize the personal data you hold. You should know all about the personal data that comes to you from a user, how is stored — by you, or the processors you’re working with, and if it complies with GDPR. You should always work with trusted processors. You should have a person in charge of GDPR to do the audit. Additionally, invest in training your personnel on GDPR.
- Explicitly request consent. You should assess the way you collect information, and if the user gives explicit consent to you collecting and managing her/his data. Add double opt-ins when asking for information, and present the way you’re going to use the data in layman’s terms and explicitly.
- Announce the changes in your private information. You should audit your current privacy notices, and change them in order to be GDPR compliant. Afterward, you should announce your users about the changes. Inform them about collecting cookies by providing details about the data that is taken, and a button for accepting the conditions. Furthermore, provide an opt-out option. You should have special pages on your website dedicated to cookies and confidential policies. The cookies page should contain the name of the cookies, their purpose (traffic analysis), the provider, type, and expiration date.
- Create an access request procedure. Users will want to know what personal data you collect. You should create a procedure of how you handle requests, and how you will deliver the request. Create an easily downloadable document with the entirety of personal data of each of your users.
- Create a data breach procedure. You should have in place a procedure for detecting breaches, resolving them, and how the users are informed about them — depending on the breach risk level.
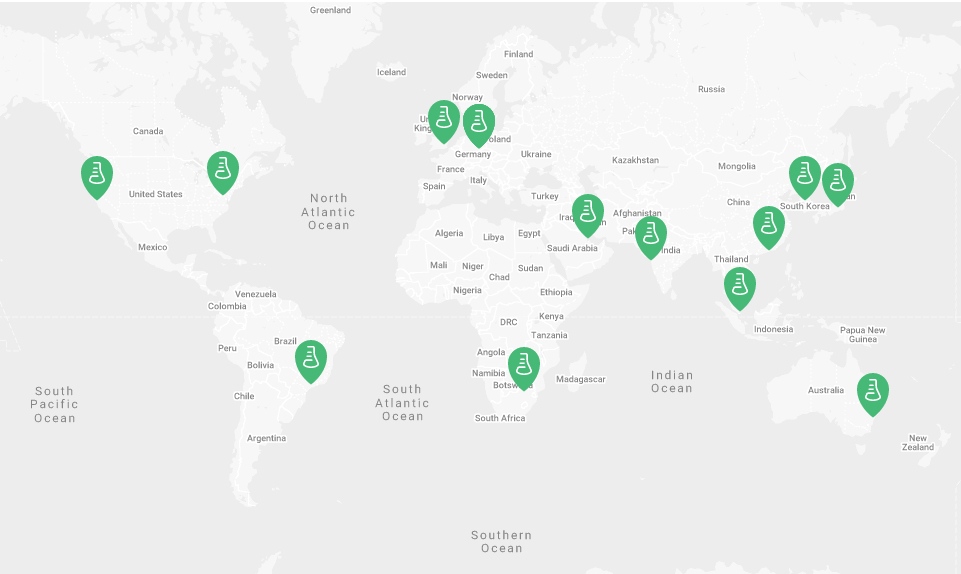
#Who is in charge of the GDPR regulation in your country?
Every country has a governing force that is in charge of implementing the GDPR compliance legislatures. The governing bodies are the following:
#The Near Future
Changes in terms of personal data were inevitable. We’ve seen marketing campaigns literally stalking users, or tricking them into giving their information, and we’ve seen high profile brands giving access to third party users to access their users’ information and manipulate public opinion. It felt like end users were completely vulnerable to the dark pattern on the web.
This regulation plans to change it all. Like we’ve said at the beginning of the article, the impact it will have will be measured once GDPR will be enforced. Yet, we’re certain that this is the beginning of a more ethical Internet consumption.